Software Vulnerability Management
Identify & mitigate software vulnerabilities with ease
Most security exploits use vulnerabilities that have been documented for over a year, but many organizations don’t have sufficient resources to address them. Support vulnerability identification and remediation with Flexera and prioritize your next steps based on reliable intelligence from Secunia Research.
Recommended Products
Close the risk window on cyber attacks
Stay secure
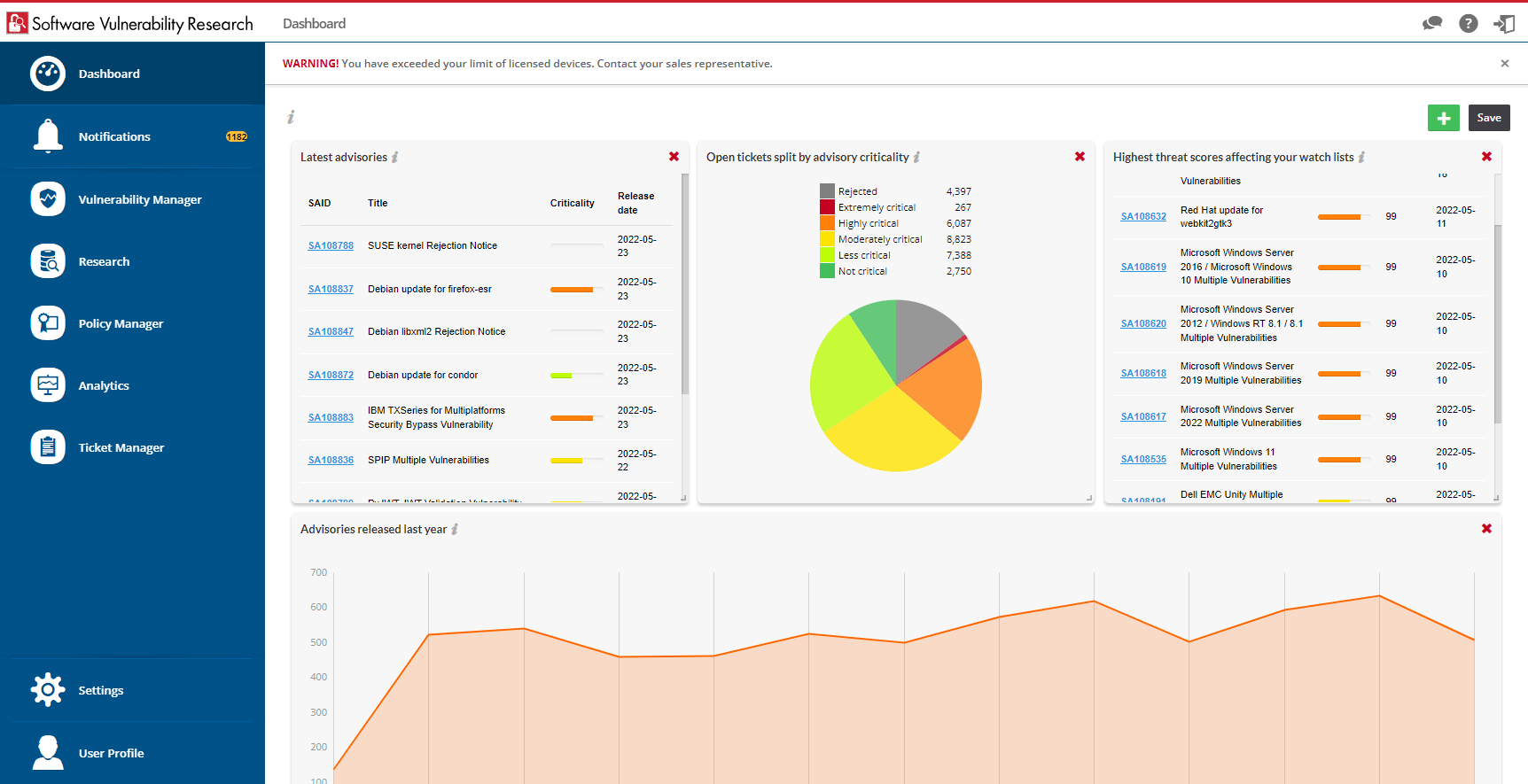
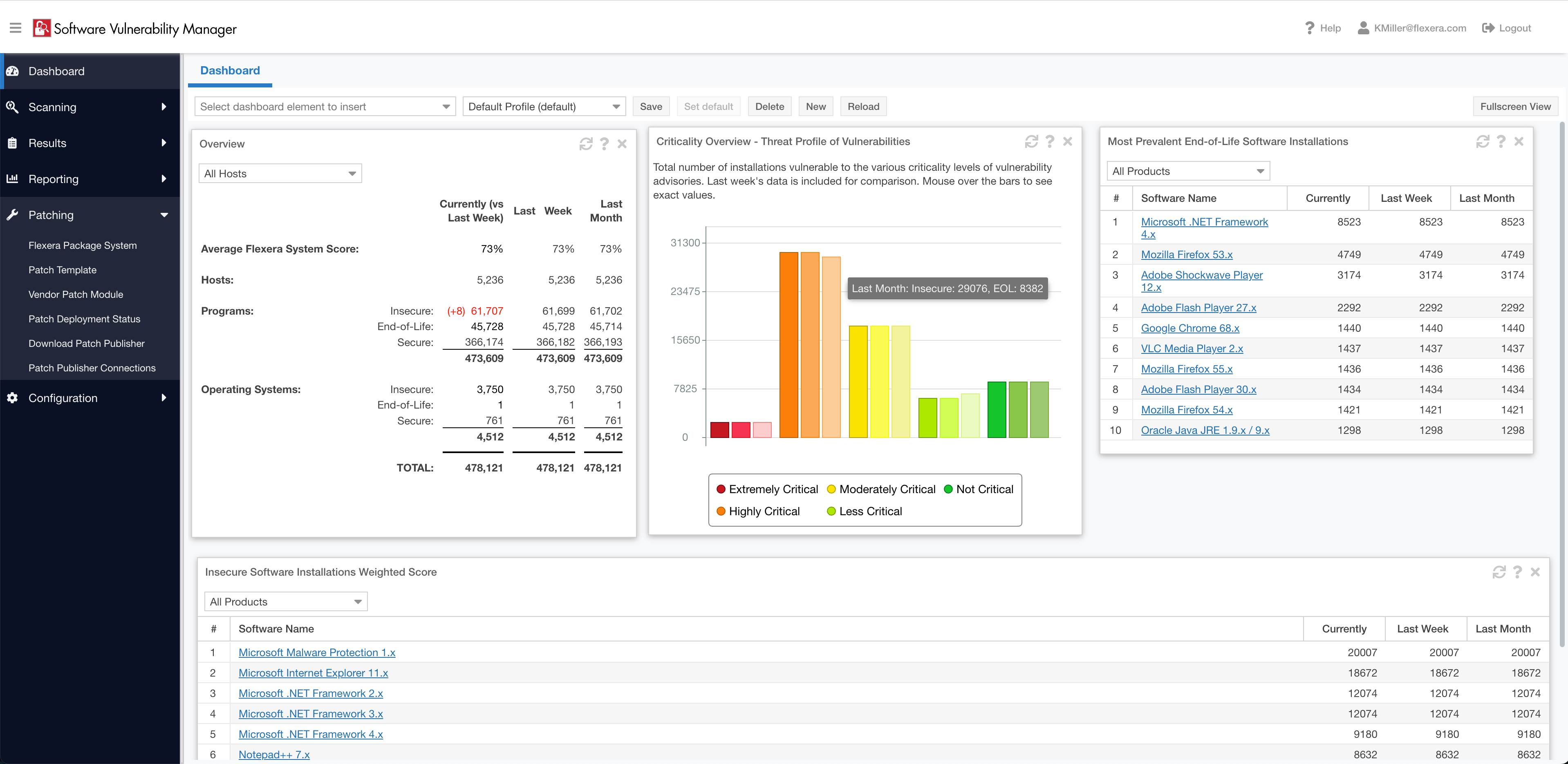
Control your entire software vulnerability management lifecycle
To effectively mitigate risk, you want to build processes that connect policies with software vulnerability and patch management activities. Flexera helps you address critical vulnerabilities with a clear picture of your environment and a full understanding of how vulnerabilities and patches are managed.
Collaborate effectively
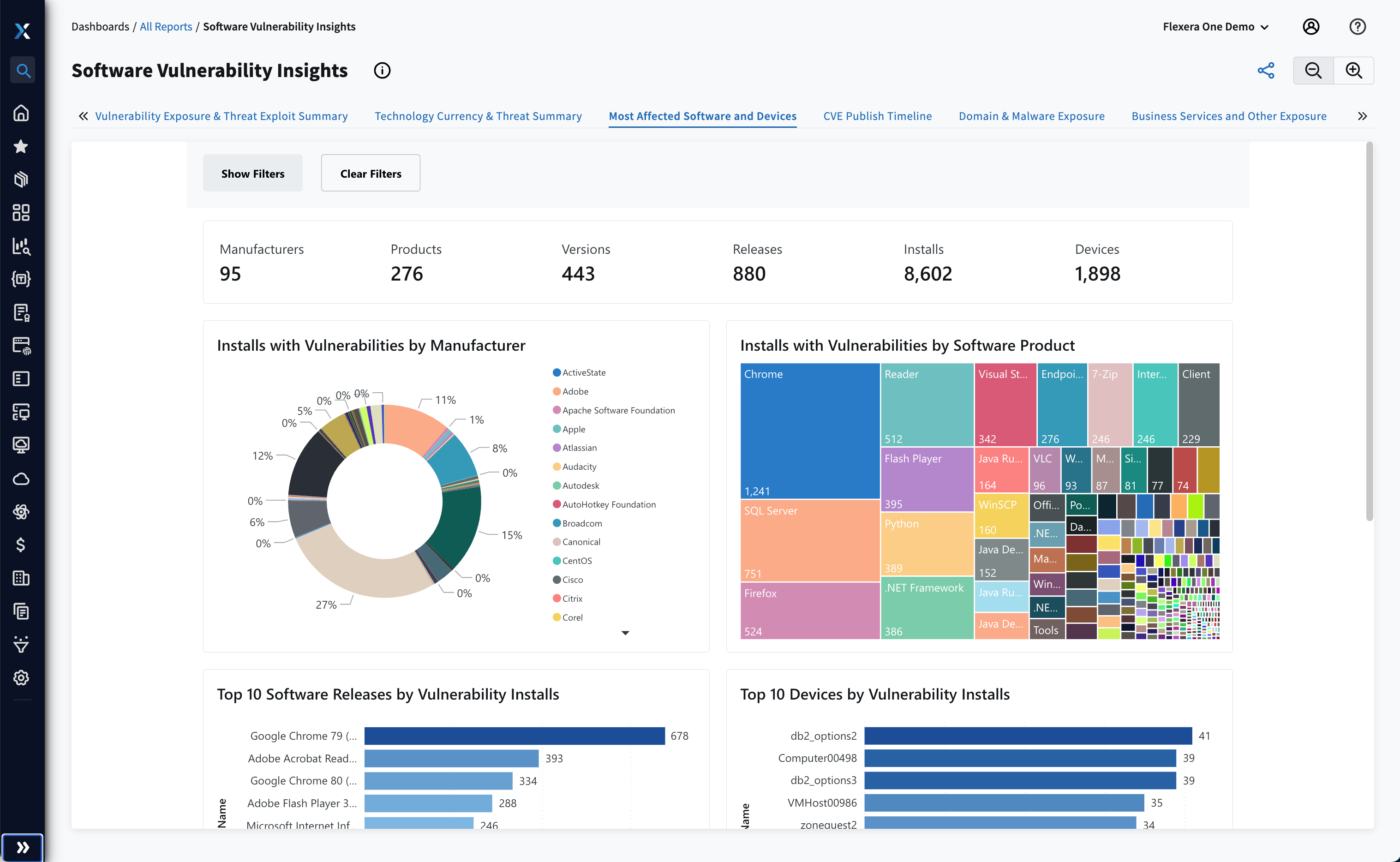
Gain visibility into all your software
ITAM professionals can enable security teams to quickly find a software title or version that has reported vulnerabilities. This makes it easier to run vulnerability checks on applications prior to deployment and ensures that unnecessary risk isn’t introduced into your environment, bolstering quality initiatives and helping cleanse software catalogs.
Make prioritization a priority
Connect assessment and patching to remediate efficiently
Discover and track more applications across Windows, Mac and Linux platforms than any other provider with Flexera. Leverage Secunia Research security advisories to simplify your prioritization process with criticality, threat scoring, impact, attack vectors and more details to find solutions that work best for your organization.
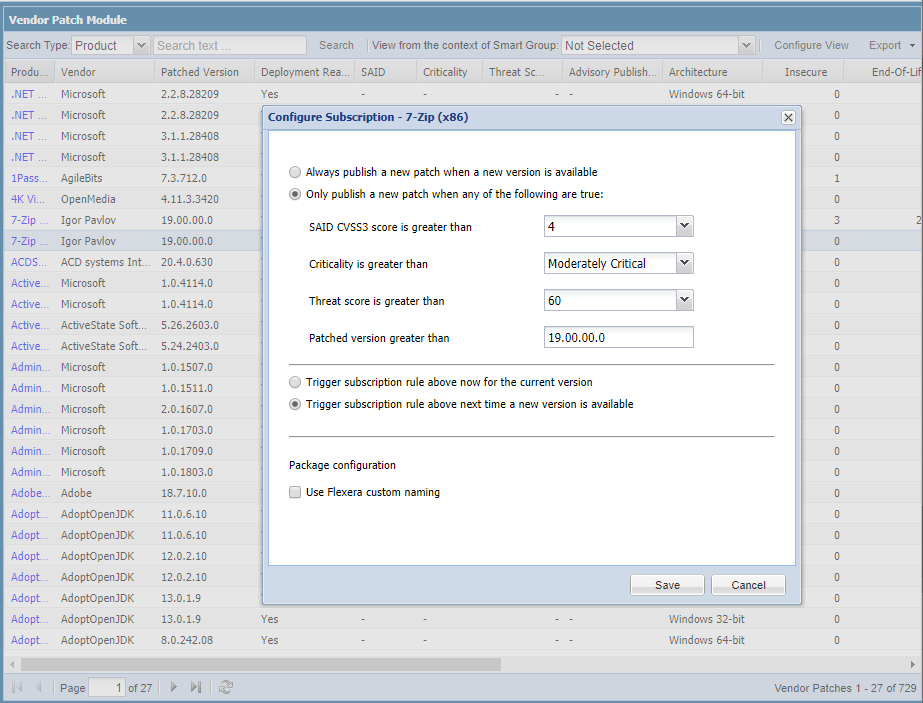
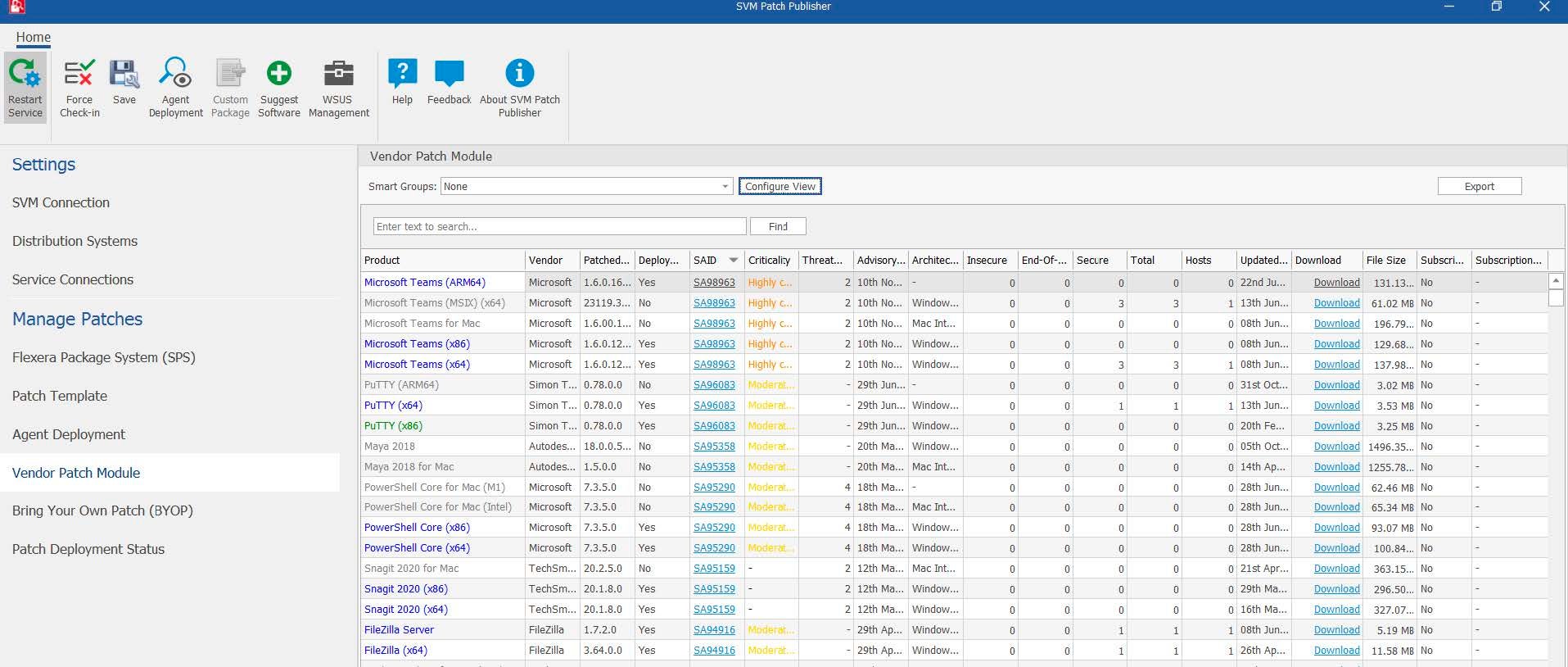
Intelligent automation
Time and resources are finite
Reduce the time-to-resolution window and drive routine patching with automation. Focus on more complex applications while putting the routine on autopilot. Choose which applications to automate and set conditions to publish only the versions you determine to be most impactful.
Improve risk mitigation
Prioritize smarter with threat intelligence
Only 6 to 8 percent of vulnerabilities lead to an exploit that could damage your organization if not patched. Bolster the insights that enable effective prioritization with threat intelligence that helps you determine which vulnerabilities are most likely to be exploited. Flexera’s threat score metric associates this valuable insight with your unpatched products to help ensure you focus on the patches that most affect your environment.
More than 18,000 vulnerability emerge every year
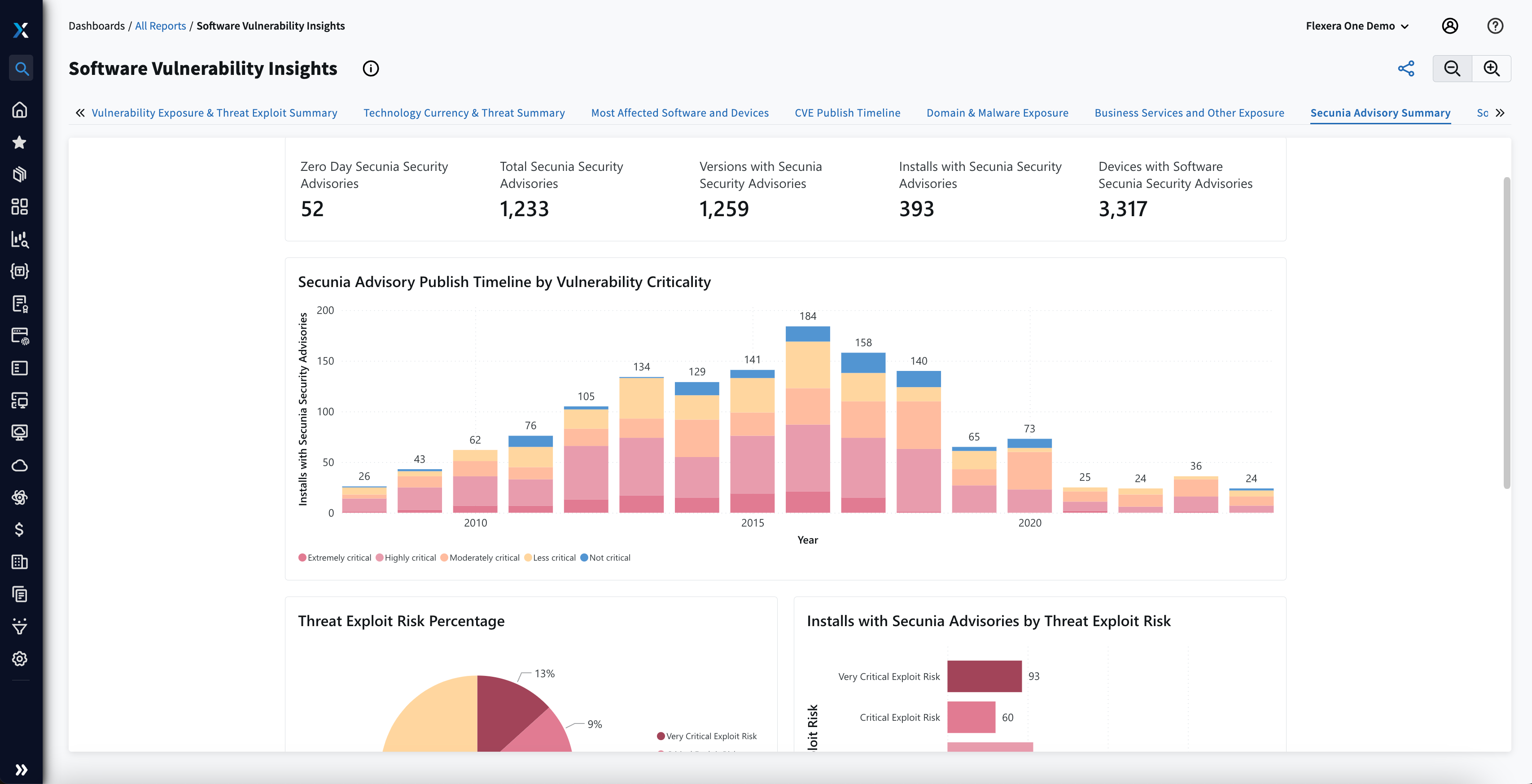
Sharpen vulnerability remediation
Intelligence you need when you need it
Maximize your vulnerability response with advisories provided by Flexera’s Secunia Research team and cover all security vulnerabilities associated with a specific version of a product. Patch those most likely to be exploited by leveraging a consistently updated scoring system. With Flexera, know the impact, the attack vector and the source, and get more specifics to understand the context in your environment.
Flexera has become fundamental to our patch management regime. We now have oversight that we’ve never had before. What was a complex, difficult, and time-consuming process is now more structured, prioritized and focused. We’re in a better position than we’ve ever been.
Frequently asked questions
Software vulnerability is a structural or design flaw present in a software application that can be exploited by attackers to compromise the security and functionality of the system, network or data with which it interacts. To learn more, visit our glossary here.
Implementing a comprehensive strategy to mitigate software vulnerabilities and safeguard your organization can present a number of obstacles. Common challenges include resource constraints, complexity of systems, third-party dependencies, legacy systems, time sensitivity, skills shortages and regulatory compliance. Click here to learn more.
Ensuring a robust plan for managing software vulnerabilities bolsters your overall cybersecurity posture, reducing the risk of data breaches, unauthorized access and service disruptions. By preventing potential damage, your company safeguards its reputation, customer trust and regulatory compliance.
To discover more about how to protect your enterprise from software vulnerabilities, join our upcoming roundtable discussion.
Informing IT, Transforming IT
Industry insights to help keep you informed
Efficiently prioritize vulnerability mitigation
We’re here to help you focus the time you spend remediating software vulnerability with our software vulnerability management expertise