I recently returned from another successful FS-ISAC Spring summit where I shared our thoughts on the current state of software vulnerabilities with the advisory board, comprised of about 200 people. We put together dedicated and exclusive analysis from our Secunia Research, and mixed it with some highlights from our Annual Vulnerability Report and other data coming from our Open Source Software Composition Analysis experience in the field, but, hands down, the majority of the people that approached me after the 20 minute talk, came to chat about Technology Asset Management.
And looking back, all I did was to highlight the importance of Software and Hardware Asset Management for proper implementation of security at any level. In all best practices, frameworks and regulations, the first few recommendations to implement cyber security controls talk about understanding a proper inventory of software and hardware. Without this, there is not much a next-gen AI firewall, sophisticated CASB tools or flux capacitors can do to protect the organization’s assets. If you are still not convinced, look at this table of the top cyber security frameworks, and a map to where they talk about SAM and HAM:
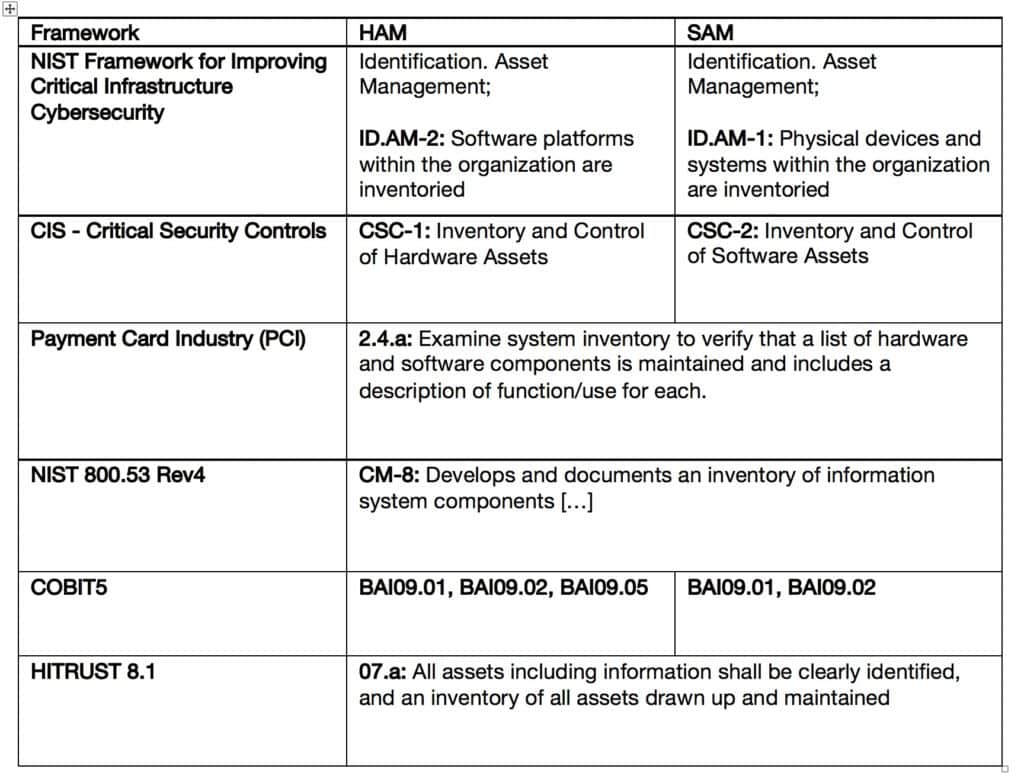
Security Frameworks and their reference to Technology Asset Management
Proper technology asset management helps reduce risk in the form of unlicensed software, unmanaged applications, end-of-life and vulnerable applications just to name a few. Having the visibility of the real software and hardware estate allow for decision making on areas that have legal, economic and security implications, but the keyword is still visibility, and that is affected by size and complexity of the organization. This is where proper tools and processes need to be implemented by following best practices like ISO/IEC 19770-1, for example, and this is where our expert team at Flexera and our partners can help, because TAM doesn’t have to be so complicated.